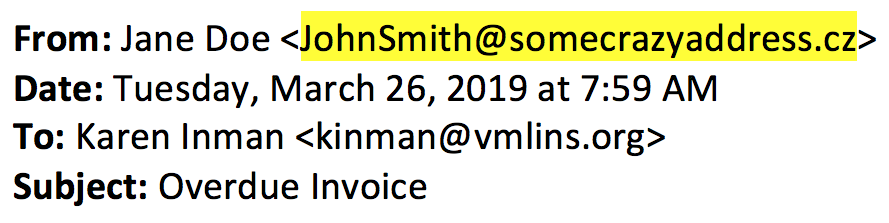
A common technique used by scammers is to send an email that looks like it is coming from a legitimate sender; this practice is known as spoofing. Many times, the spoofed email has clues in it to help the receiver identify that it is not coming from the person they claim to be.
The most common clue is that the email address does not correspond to the name of the person in the “From” line. As demonstrated below, the sender is allegedly Jane Doe, but the email address indicates it is from someone named JohnSmith.
While it is important for email recipients to be diligent and look for clues of a fraudulent sender, people make mistakes. And, spammers are pretty sneaky – they often put an email address that is very close (maybe off by one letter) from the real email address.
Having strong email filters to identify these messages as potential junk and either quarantine the messages or send them to a junk folder where the reader knows to apply a little more rigor when looking at the emails is one way to mitigate being a victim of fraudulent emails.
However, spam algorithms are error prone and need to constantly evolve to respond to the changing tactics of spammers.
How can readers recognize these fraudulent emails? What can your organization do to filter out these emails before they reach a user’s inbox? How can you cut down on emails other organizations receive from you that have been spoofed to look like legitimate messages?
While most email providers have algorithms to help identify spam messages, there are limited technologies available to identify and filter out spoofed messages. The tools that are available require both the sender and receiver to implement tools to effectively provide a form of two-factor authentication. The tools to achieve this extra layer of authentication are called DKIM and DMARC.
Domain Keys Identified Mail (DKIM) allows the sender to set up a special key that is sent in the email header that is read by the receiving email provider to allow them to validate the sender is who they say they are. The DKIM record also transmits instructions to the receiving email system on how to handle emails that are not validated. This information is transmitted behind the scenes, so it is transparent to the senders and receivers of the email. DKIM will help filter out some emails but does not fully address spoofed emails.
To add the next layer, organizations can enable Domain-based Message Authentication, Reporting & Conformance (DMARC). DMARC allows receivers to leverage DKIM more effectively to validate the authenticity of the messages that are being received and take action based on the senders published policies based on that validation.
Other than a small amount of effort on the part of information technology resources, there are no additional costs for an organization to implement DKIM and DMARC, and the potential to filter out spoofed messages is a great benefit. More information about setting up DKIM and DMARC can be found at: www.dkim.org and www.dmarc.org.

